Call: (02) 8681 9790 (02) 8818 4883
Please Call for price
RG-WS6008
Order Now
Call for Price
RG-WS6008 High-Performance Wireless Controller
- It can manage up to 32 APs by default and a maximum capacity of 448 APs with license upgrade.
- Seamless integrated with Ruijie Wireless Intelligent Cloud Service (WIS) that provides AI-based wireless optimization round the clock for your Wi-Fi service.
RG-WS6008 High-Performance Wireless Controller
The RG-WS6008 high-performance wireless access controller (AC), developed by Ruijie Networks, is targeted for high-speed wireless networks. It can be deployed on a Layer 2 or Layer 3 network without any architecture or hardware device changes, delivering seamless and secure control over wireless networks.
The RG-WS6008 can manage up to 32 wireless access points (APs) by default. With licenses for capacity expansion, it can manage a maximum of 224 generic APs or 448 wall-mounted APs.
Through powerful centralized and visualized management and control over wireless networks, the RG-WS6008 can significantly simplify construction and deployment of wireless networks.
The RG-WS6008, adopting enhanced security and clustering technologies, offers identity-based networking services. Multiple ACs in a cluster can share a user database, allowing clients to seamlessly roam in different areas of a network. The cluster design guarantees the security and session integrity during roaming and smooth interaction of data and voice over Wi-Fi applications.

Features
Smart Wireless Experience Intelligent Client Identification
The built-in Portal server of the RG-WS6008 can intelligently identify clients based on characteristics of the clients, and adaptively respond with a portal authentication page of the matching size and layout. Intelligent client identification eliminates the need to drag and resize a window, delivering users with a better intelligent wireless experience. This technology supports mainstream intelligent client operating systems including Apple iOS, Android, and Windows.
Fair Client Access
The RG-WS6008, together with Ruijie Networks’ APs, provides the same access time for clients in compliance with IEEE 802.11g, 802.11n, 802.11ac, 802.11ax, and other standards. This resolves issues such as the long latency, slow speed, and low performance of APs caused by outdated NIC in clients or long distance between clients and APs. This also effectively improves the performance of low-speed clients, and ensures consistent and good wireless experience at the same location regardless of the client type.
Client Access Optimization
It can be used with WIS Cloud to monitor network-wide client behaviors and operating status, and obtain information such as the client signal strength and channel utilization through APs. With Wi-Fi client identification and access planning, it solves problems such as roaming stickiness and remote association, and achieves load balancing and improved network-wide wireless performance.
Intelligent Load Balancing
In a high-density environment, the RG-WS6008 can intelligently distribute clients connected to APs in real time based on the number of clients and traffic on each associated AP. This balances the traffic load, increases the average client bandwidth and QoS, and improves the availability of network connections. In addition to client-based and traffic-based intelligent load balancing, the RG-WS6008 also supports load balancing based on the frequency band. Most Wi-Fi devices use the 2.4 GHz band by default, but can achieve increased throughput in the 5 GHz band (IEEE 802.11a/n/ac/ax-compliant). Load balancing based on the frequency band enables dual-radio-capable clients to preferentially use the 5 GHz frequency band and guarantees a high-speed wireless experience for clients.
High Performance and Reliability
High Performance for Small- and Medium-sized Networks
The RG-WS6008 runs the RGOS system and can manage up to 7,168 clients and 448 APs simultaneously. It has a high-performance 4-core CPU. It can be used for small- and medium-sized networks, to set up a secure, efficient, and easy-to-manage wireless network.
Centralized/Distributed, Integrated, and Intelligent Forwarding
The RG-WS6008 can be deployed on a Layer 2 or Layer 3 network without changing the original network architecture. It constitutes an overall switching architecture with APs to facilitate control and processing of traffic on all APs. The intelligent local forwarding technology eliminates the traffic bottleneck of an AC.
With local forwarding technology, the RG-WS6008 can flexibly configure data forwarding modes for connected APs. That is, the RG-WS6008 can determine whether data needs to be forwarded through itself, or directly enters the wired network for local forwarding based on the network SSID and VLAN planning.
The local forwarding technology enables the RG-WS6008 to forward data that is sensitive to the delay and requires real-time high-performance transmission through a wired network. Facing high throughput of 802.11ac- and 802.11ax-compliant clients, this technology can greatly reduce the traffic forwarding pressure of the RG-WS6008 to better adapt to future wireless networks such as high definition (HD) Video on Demand (VoD) and Voice over Wireless Local Area Network (VoWLAN) transmission.
Intelligent RF Management
The RG-WS6008 enables an AP to perform on-demand RF scanning on a wireless network. The RG-WS6008 can scan wireless frequency bands and channels, identify unauthorized APs and wireless networks, and notifies network administrators of alarms, providing all-round protection in a security-sensitive environment.
Moreover, the RG-WS6008 can control the RF scanning function of APs in real time, and measure the signal strength and interference. It can dynamically regulate the traffic load, transmit power, RF coverage area, and channel allocation using software tools to maximize the AP coverage and capacity.
Network-wide Seamless Roaming
The RG-WS6008 supports the best-in-class AC cluster technology. Multiple RG-WS6008 controllers in a cluster can synchronize online connection information and roaming records of all clients in real time. When a client roams, the client can roam freely on the entire network based on shared client information and authorization information in the cluster. Furthermore, the client can roam seamlessly and securely, and keep the IP address and authentication status unchanged, so as to achieve fast roaming and voice support.
Abundant QoS Policies
The RG-WS6008 supports abundant QoS policies such as bandwidth limiting in multiple modes and preferential bandwidth guarantee for key data applications.
The RG-WS6008 supports bandwidth limiting based on the WLAN, AP, and STA, and provides Wi-Fi Multimedia (WMM) that defines priorities for different service data. Therefore, it implements immediate and quantitative transmission of audio and video data, and guarantees smooth application of multimedia services.
The multicast-to-unicast technology supported by the RG-WS6008 solves the video freezing problem caused by packet loss or long latency in Video on Demand (VoD) and other multicast applications on a wireless network. It enhances the experience in the use of multicast video services on a wireless network.
Wireless IPv6 Access
The RG-WS6008 fully supports IPv6 features, ensuring IPv6 forwarding on wireless networks. IPv4 and IPv6 clients can automatically connect to the RG-WS6008 through tunnels to provide IPv6 services on wireless networks.
Advanced AC Virtualization
The RG-WS6008 supports the cutting-edge AC virtualization technology. The technology can virtualize up to four ACs into one logical AC, realizing high reliability and capacity expansion without additional hardware devices.
- Simplified topology: All member ACs of the logical AC use the same IP address. Regardless of whether the logical AC connects to an AP or an authentication server, there is no need to assign an IP address to each member AC.
- Simplified configuration: Multiple member ACs can be managed as one AC. Any configuration of the master AC can be automatically synchronized to all member ACs.
- High reliability: N+M hot standby is supported. The breakdown of any AC will not affect the overall system.
- Smooth capacity expansion: The AP and client capacity can be expanded by adding a physical AC.
- Licensesharing: A license installed on any member AC of the logical AC can be shared by other member ACs.
Advanced Application Recognition and Policy Control
To simplify network management and protect wired and wireless network access, the RG-WS6008 supports advanced application identification and policy control technologies. The RG-WS6008 can be configured with different user objects, network objects, and VLANs for flexible policy control. In this case, there is no need to configure separate network policies for SSIDs, VLANs, and other objects.
Wired and wireless traffic is transmitted to the RG-WS6008 through the centralized/distributed, integrated, and intelligent forwarding technology, and then is managed by using application identification and control policies.
The RG-WS6008 supports application recognition and application-level QoS mapping technology for wireless clients. The RG-WS6008 in centralized forwarding mode applies Deep Packet Inspection (DPI) to packet characteristics to support over 2,500 applications. It can identify applications, collects statistics on applications, and employs QoS mapping, helping you understand the application usage on the network. Then QoS can be performed for application traffic.
For mainstream web BBS sites and search engines, the RG-WS6008 can audit and filter user posts and search contents, and allow or block data flows based on policies.
Flexible and Comprehensive Security Policies
Local Authentication
The RG-WS6008, with a built-in local user database and a built-in Portal server, authenticates wireless clients locally through web authentication. Local authentication eliminates the need to deploy an authentication server such as the external Portal server or RADIUS server. Moreover, this authentication mode simplifies the entire network architecture and greatly reduces the network construction cost, meeting requirements for secure access to small- and medium-sized wireless networks.
Client Data Encryption and Security
The RG-WS6008 supports a full range of data security protection mechanisms, including Wired Equivalent Privacy (WEP), and Temporal Key Integrity Protocol (TKIP), to ensure data transmission security on wireless networks.
Standard Communication Protocols
The RG-WS6008 communicates with APs over Control and Provisioning of Wireless Access Points (CAPWAP) tunnels and employs Datagram Transport Layer Security Version 1.0 (DTLS 1.0) for encrypted communication. This achieves isolation from a wired network and ensures confidentiality of real-time communication between the RG-WS6008 and APs. Additionally, the RG-WS6008 can use CAPWAP to control third-party APs in the future, facilitating network expansion as well as protecting existing investment.
Virtual AP Technology
With the virtual AP technology, the RG-WS6008 can allocate multiple SSIDs on a network. Network administrators can separately isolate and encrypt subnets or VLANs using the same SSID, and can configure the separate authentication method and encryption mechanism for each SSID.
AP Virtualization Technology
This technology enables one physical AP to be virtualized into multiple virtual APs, which can be managed by different wireless access controllers. Paired with Ruijie Networks’ APs that has multiple uplink physical ports, the RG-WS6008 can isolate wireless data of different virtual APs on the same physical AP, realizing exclusive use of the private network and ensuring high security of critical services. For a physical AP with a single uplink port, AP virtualization technology allows the WLAN to be shared by multiple ISPs in public places such as airports and shopping malls. This fully utilizes AP, significantly reduces the cabling cost, and eliminates interference caused by excessive APs.
RF Security
The RG-WS6008 can be flexibly configured with the RF probe scanning mechanism to discover unauthorized APs or other RF interference sources in real time. It pushes corresponding alarms to the network management system (NMS) in real time, so a network administrator can monitor potential network threats and usage in each wireless environment at any time.
The RG-WS6008 supports advanced spectrum analysis and Wireless Intrusion Detection System (WIDS). It can use WIDS to detect malicious user attacks and intrusions in the early time, helping network administrators to proactively identify potential risks on a network and provide proactive defense and early warning against wireless attackers in the first instance.
Virus and Attack Prevention
The RG-WS6008 has various built-in security mechanisms to effectively protect a network against virus and network traffic attacks, reject unauthorized network access, and allow access from authorized clients. The security mechanisms include binding of IP addresses, MAC addresses, WLANs, and other elements, hardware ACL, and data stream-based rate limiting, so the RG-WS6008 is suitable for campus, hospital, and enterprise networks where access control of guests is strengthened and access of unauthorized clients is restricted.
Secure Client Access
The RG-WS6008 supports web authentication. Clients can complete the authentication process by using a browser.
It supports 802.1X authentication on clients to guarantee network security. Moreover, it ensures host security because the 802.1X authentication client is embedded on a host for access control. Unlike web authentication, 802.1X authentication is applicable to security-sensitive areas. Furthermore, IP addresses, MAC addresses, WLANs, and other elements can be bound after authentication. This ensures that only authorized clients can access the network.
Multiple Easy-to-Use Authentication Modes
The RG-WS6008 supports conventional web authentication and 802.1X authentication for monitoring network access behaviors. It also provides convenient authentication modes for customers based on actual scenarios, such as MAC authentication bypass (MAB), and SMS-based authentication.
When connecting to a network through MAB authentication, a wireless client only needs to enter the username and password upon first login. The username and password are no longer required when the wireless client is restarted and connected to the network.
When a guest accesses a wireless network through SMS-based authentication, an authentication page pops up. On the authentication page, the guest can register an account using the mobile number, and accesses the Internet using the username and password in the SM received.
Anti-ARP Spoofing
The ARP inspection function can effectively prevent increasing ARP gateway and ARP host spoofing attacks on a network, so as to ensure normal network access. Automatic IP-MAC binding can greatly save the labor cost and simplify management in dynamic or static IP allocation mode. An attacker may maliciously use scanning tools to flood ARP packets, which occupy network bandwidth and result in network congestion. To address this issue, the RG-WS6008 uses ARP rate limiting to control the rate of sending ARP packets.
Rogue AP Containment
Rogue AP containment can effectively detect unauthorized APs on a wireless network. The RG-WS6008 can instruct an AP to send a probe packet to surrounding APs and wait for a response. It can detect the unauthorized AP that does not send a response packet, thereby ensuring network-wide security.
DHCP Security
DHCP snooping enables the RG-WS6008 to allow only DHCP Reply messages from trusted interfaces, preventing a private DHCP server without the permission of an administrator. This is because the private DHCP server seriously affects IP address allocation and management, resulting in network access failures. With DHCP snooping configured, the RG-WS6008 can dynamically check source IP addresses of ARP packets to prevent ARP spoofing attacks and source IP address spoofing attacks in the environment in which the DHCP server dynamically allocates IP addresses.
Management Information Security
Through the Secure Shell (SSH) and Simple Network Management Protocol version 3 (SNMPv3), the RG-WS6008 encrypts management information in Telnet and SNMP processes, ensuring information security of management devices and preventing hackers from attacking and controlling devices. Telnet access control based on the source IP address means fine-grained device management and control. With this function, only the devices with IP addresses configured by administrators can connect to the RG-WS6008, enhancing network management security.
Rich Management Policies
Multiple Management Modes and Unified Management Platform
The RG-WS6008 supports the CLI and other management modes to implement centralized, effective, and low-cost planning, deployment, monitoring, and management of network-wide APs. The RG-Cloud, a unified management platform for wired and wireless networks developed by Ruijie Networks, manages APs uniformly. The RG-WS6008 together with WIS Cloud implements various wireless network management functions, including topology generation, AP working status monitoring, online client status monitoring, network-wide RF planning, client locating, security alarm, link load and device utilization monitoring, roaming record, and report output. The RG-WS6008 allows an administrator to monitor and manage the running status of the entire network in a data center.
Hierarchical AC Management
The h supports hierarchical AC management. A central AC uniformly manages hundreds of branch ACs, substantially simplifying wireless device management in the scenario with the headquarters and many branches. Hierarchical AC management has the following features:
- Unified management: The central AC uniformly upgrades the software of branch ACs and APs, and monitors the running status of each branch AP.
- High reliability: When a branch AC fails, branch APs can be taken over by the central AC, realizing fast failover and improving the reliability of the branch wireless network.
- License sharing: The branch AC can share the license installed on the central AC as required. A license can be installed on the central AC, and shared by all branch ACs on a network.
Eweb Management
The RG-WS6008 provides the Eweb, on which O&M personnel can complete wireless configuration easily, and manage the wireless network uniformly. On the Eweb, O&M personnel can manage APs and connected clients, limit the client rates, and restrict network access behaviors of the connected clients. With the Eweb, O&M personnel can plan, manage, and maintain wireless networks conveniently.


Specifications
| Dimensions and Weight | RG-WS6008 |
| Unit dimensions (W x D x H) | 440 mm x 200 mm x 43.6 mm (17.32 in. x 7.87 in. x 1.72 in.) |
| Shipping dimensions(W x D x H) | 560 mm x 470 mm x 380 mm (22.05 in. x 18.5 in. x 14.96 in.) |
| Rack height | 1 RU |
| Unit weight | 2.9 kg (6.39 lbs) |
| Shipping weight | 16.47 kg (36.31 lbs) |
| Ports | RG-WS6008 |
| Fixed service port | 6 x 10/100/1000BASE-T ports 2 x 1GE SFP/RJ45 combo ports |
| Fixed management port | 1 x RJ45 console port 2 x USB ports |
| Status LED | 1 x system status LED 1 x power status LED 10 x service port LEDs |
| Button | 1 x Reset button ● Press the button for shorter than 3 seconds. Then the device restarts. ● Press the button for longer than 3 seconds. Then the device restores to factory settings. 1 x power switch |
| Power Supply and Consumption | RG-WS6008 |
| Maximum power consumption | 40 W |
| Input power supply | 1 x 40 W built-in power module |
| Input voltage | 100 V AC to 240 V AC, 50 Hz to 60 Hz |
| Input current | 1.5 A (maximum RMS current) |
| Output voltage | 12 V/3.33 A |
| Environment and Reliability | RG-WS6008 |
| Temperature | Operating temperature: 0°C to 45°C (32°F to 113°F) Storage temperature: –40°C to +70°C (–40°F to +158°F) Note: At an altitude in the range of 3,000–5,000 m (9,842.52–16,404.20 ft.), every time the altitude increases by 166 m (544.62 ft.), the maximum temperature decreases by 1°C (1.8°F). |
| Altitude | Operating altitude: 0 m to 3,000m (0 ft. to 9,842.52 ft.) Storage altitude: 0 m to 3,000m (0 ft. to 9,842.52 ft.) |
| Humidity | Operating humidity: 10% RH to 90% RH (non-condensing) Storage humidity: 5% RH to 95% RH (non-condensing) |
| Fan | Fan speed adjustment Fan fault alarm |
| Acoustic noise | < 78 dB |
| Mean Time Between Failure (MTBF) | 200,000 hours (22 years) at the operating temperature of 25°C (77°F) |
Software Specifications | RG-WS6008 |
| WLAN | |
| Default number of manageable APs | 32 Note: The default number of APs that can be managed by the RG-WS6008 is subject to the AP model. See the Ordering Information for details. |
| Maximum number of configurable APs | 2,048 |
| Maximum number of manageable APs | 448 Note: The maximum number of APs that can be managed by the RG-WS6008 is subject to the AP model. See the Ordering Information for details. |
| Maximum number of manageable STAs | 7,168 Note: The maximum number of STAs that can be managed by the RG-WS6008 is subject to the network environment. Contact technical support team for details. |
| WLAN service | Maximum number of WLAN IDs: 2,048 Maximum number of associated STAs per WLAN: 7,168 |
| Intra-AC roaming handoff time | < 50 ms |
| Maximum number of virtualized ACs | 4 |
| Number of concurrent CAPWAP data channels | 2,688 |
| Routing and Switching | |
| Number of MAC address entries | 32,768 |
| Number of VLANs | 4,096 |
| Number of ARP entries | 32,768 |
| DHCP address pools | Number of IPv4 address pools: 2,000 Number of IPv4 addresses: 24,576 Number of IPv6 address pools: 256 Number of IPv6 addresses: 2,048 |
| Number of routing entries | IPv4 routing entries: 8,192 IPv6 routing entries: 10,000 |
| Number of multicast entries | Static routing entries: 2,048 Multicast group routing entries: 4,096 |
| Security and Authentication | |
| Maximum number of STAs supported by the built-in Portal server | 1,500 |
| Number of ACL entries | 65,536 |
| Applicable Software Version | RG-WS6008 |
| Applicable software version | RGOS11.9(6)W1B1 or later |
| WLAN | RG-WS6008 |
| IEEE 802.11 protocols | 802.11, 802.11b, 802.11a, 802.11g, 802.11d, 802.11h, 802.11w, 802.11k, 802.11v, 802.11r, 802.11i, 802.11e, 802.11n, 802.11ac, and 802.11ax |
| CAPWAP | Layer 2 and Layer 3 topology between an AP and an AC An AP can automatically discover the accessible AC. An AP can be automatically upgraded through the AC. An AP can automatically download the configuration file from the AC. CAPWAP through NAT |
| Roaming | Intra-AC Layer 2 or Layer 3 roaming Inter-AC Layer 2 or Layer 3 roaming |
| Forwarding mode | Centralized forwarding Local forwarding Service-based flexible forwarding |
| Wireless QoS | AP/WLAN/STA-based rate limiting (WLAN/STA-based rate limit range: 8-261,120 in the unit of 8 Kbps. For example, if you set the value to 8, the rate limit is 8 x 8 Kbps = 64 Kbps.) Static and intelligent rate limiting based on STA quantity Fair scheduling |
| User isolation | AC-based user isolation AP-based user isolation WLAN-based user isolation |
| Reliability | AC virtualization AC failover Multi-AC hot standby (1+1 A/A and A/S hot standby, and N+1 hot standby) Multi-AC cluster (N-to-N) Remote intelligent perception technology (RIPT) Non-stop service during upgrade |
| STA management | Access control based on the number of STAs associated with the AP Access control based on the number of STAs associated with the SSID Balanced access control based on the number of STAs associated with the AP Balanced access control based on the AP traffic Band steering Configuration of the RSSI threshold in dB (Range: 0-100) Configuration of the STA idle timeout period in seconds (range: 60-86,400) |
| WLAN optimization | Adjustment of the transmit power for beacon packets or probe responses |
| RF management | Country or region code setting Manual setting of the transmit power Automatic setting of the transmit power Manual setting of the operating channel Automatic setting of the operating channel Automatic adjustment of the data rate Coverage hole compensation AP load balancing based on traffic and STA quantity Band selection Radio Frequency Interference (RFI) detection and mitigation |
| Security | RG-WS6008 |
| IPv4 security authentication | Web authentication 802.1X authentication MAB authentication SMS authentication |
| IPv6 security authentication | Web authentication |
| IEEE 802.11 security and encryption | Multi-SSID mode SSID hiding IEEE 802.11i-compliant PSK authentication WPA and WPA2 WPA3: WPA3-Personal (SAE), WPA3-Enterprise (CCMP, 128-bit), and WPA3-Enterprise (GCMP, 192-bit) WEP (WEP/WEP128) TKIP CCMP Anti-ARP spoofing |
| CPP | Supported |
| NFPP | Supported |
| WIDS | Supported |
| AP virtualization | Supported |
| Protocols | RG-WS6008 |
| IPv4 protocols | Ping and traceroute DHCP server, DHCP client, DHCP relay, and DHCP snooping DNS client NTP Telnet TFTP server and TFTP client FTP server and FTP client |
| IPv6 protocols | DNSv6 client DHCPv6 relay and DHCPv6 server TFTPv6 client FTPv6 server and FTPv6 client IPv6 CAPWAP ICMPv6 IPv6 ping Manual tunnels and automatic tunnels Manually configured IP addresses and automatically created local addresses IPv6 traceroute |
| IPv4 routing | Static routing, RIP, and OSPF |
| IPv6 routing | Static routing |
| Management | RG-WS6008 |
| Network management | SNMP v1/v2c/v3 RMON Syslog |
| Network management platform | Eweb Ruijie Cloud Wi-Fi heat map |
| User access management | Console port login, Telnet login, SSH login, and FTP upload |
| Regulatory Compliance | RG-WS6008 |
| Safety regulations | IEC 62368-1, EN 62368-1 |
| EMC regulations | EN 55032, EN 55035, EN 61000-3-3, EN IEC 61000-3-2, and ETSI EN 300 386 |
| Model | Description |
| RG-WS6008 | The next-generation wireless controller provides 6 x GE electrical ports and 2 x SFP combo ports. It supports 32 APs by default, and up to 224 licenses are available. The maximum number of APs that can be managed by the AC is subject to the AP model: ● A generic AP occupies one license. The RG-WS6008 can manage up to 224 generic APs. ● A wall plate AP occupies half of the license. The RG-WS6008 can manage up to 448 wall plate APs. ● An i-Share micro AP occupies no license. The RG-WS6008 can manage up to 448 i-Share micro APs. ● The number of licenses occupied by an i-Share master AP is subject to the model. See the ordering information in the datasheet of corresponding i-Share master AP for details. |
Explore more products when you click here.
You may also like and follow our Facebook Page: Clusterasia Corp. for more updates.
Based on 0 reviews
| 0% | ||
| 0% | ||
| 0% | ||
| 0% | ||
| 0% |
Related Products
FIBER OPTIC MICROSCOPE / OPTICAL FIBER END MAGNIFIER
FS-3 Fiber Stripper Three-port Fiber Optical Stripper Optical Fiber Stripping Pliers Wire Stripper
Miller clamp is a widely used general tool. It is mainly used for moving tube and coating of fibers, can handle most of the common application. Besides, the handle uses an ergonomic design so that it is more comfortable for long-time operation.
High quality Miller Loose Buffer Tube Stripper/Mid-Span Access Tool 0.9mm to 3.0mm Fiber Optical Stripper
- Model Number: AUA-05 stripper
- Type: Optical cable stripper, Optical Fibers
- Place of Origin: Shanghai, China
- Brand Name: DSEE
- Use: FTTH
- Warranty Time: 1 year
- Model Number:: wire stripper multi tool
- Access tube sizes: 0.9mm to 3.0mm
- key feature: Shaves precise opening to prevent fiber damage
- original country::: the U.S.A
- Use::: FTTH
- Application:: FTTH FTTB FTTX Network
- Weight:: 1.36 oz (38.5g)
- Application: FTTH
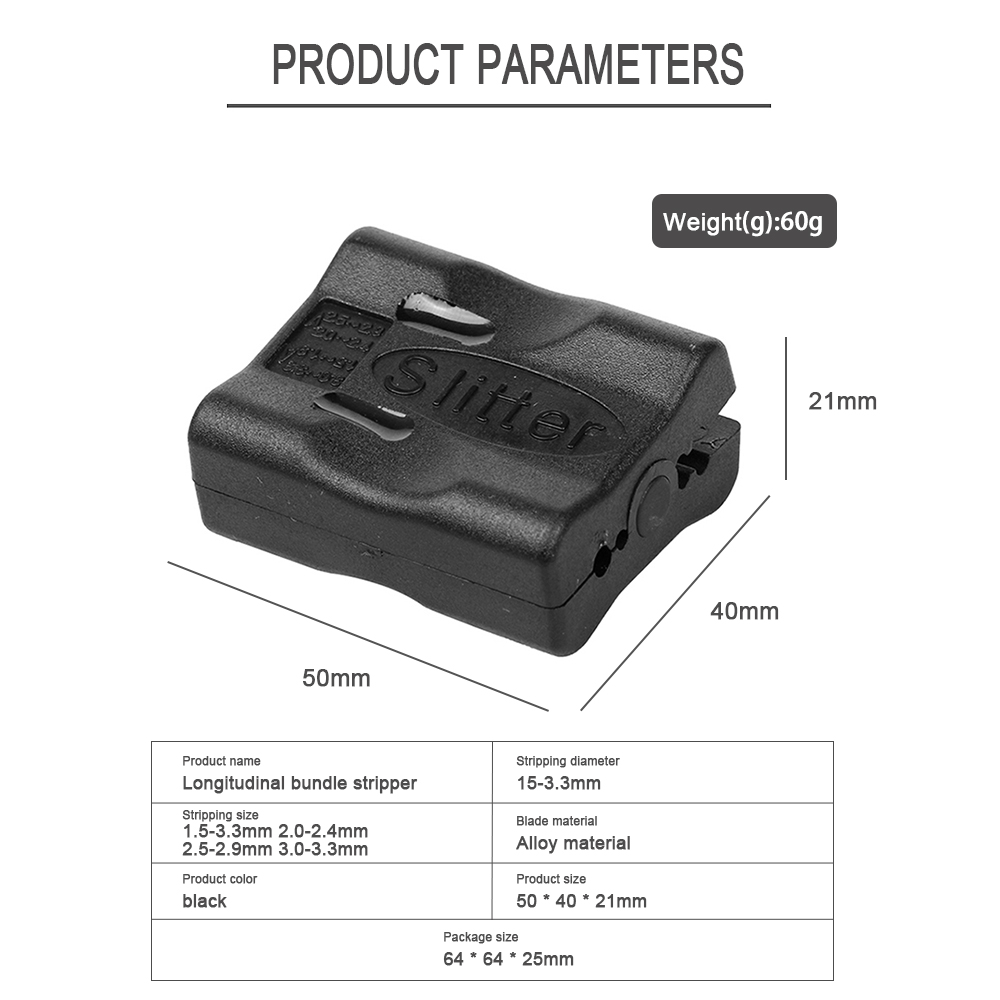
Buffer Tube slitter Longitudinal Cable Sheath Cutter
ARMOURED CABLE STRIPPER/SLITTER 8 – 28.6 MM
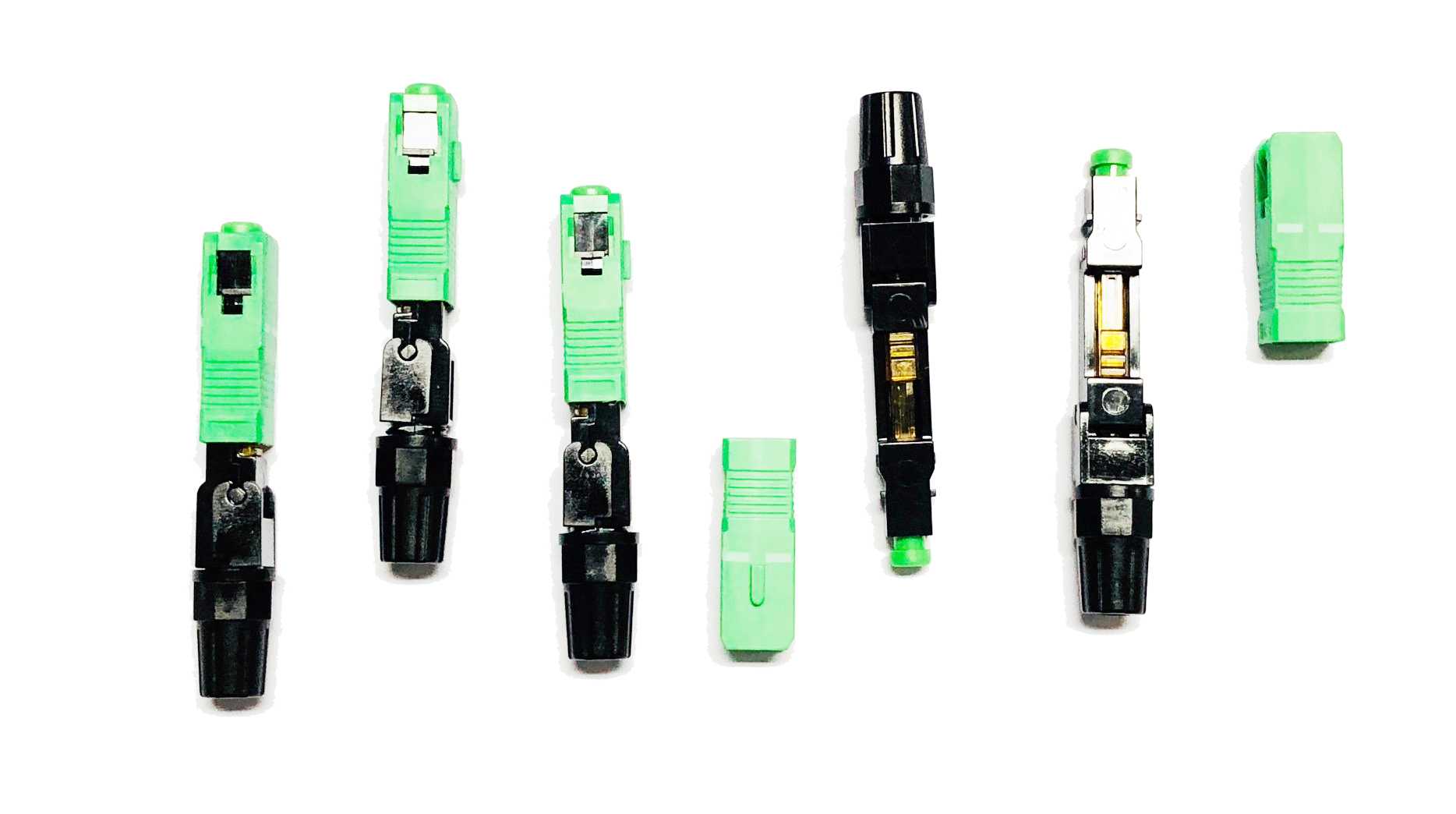
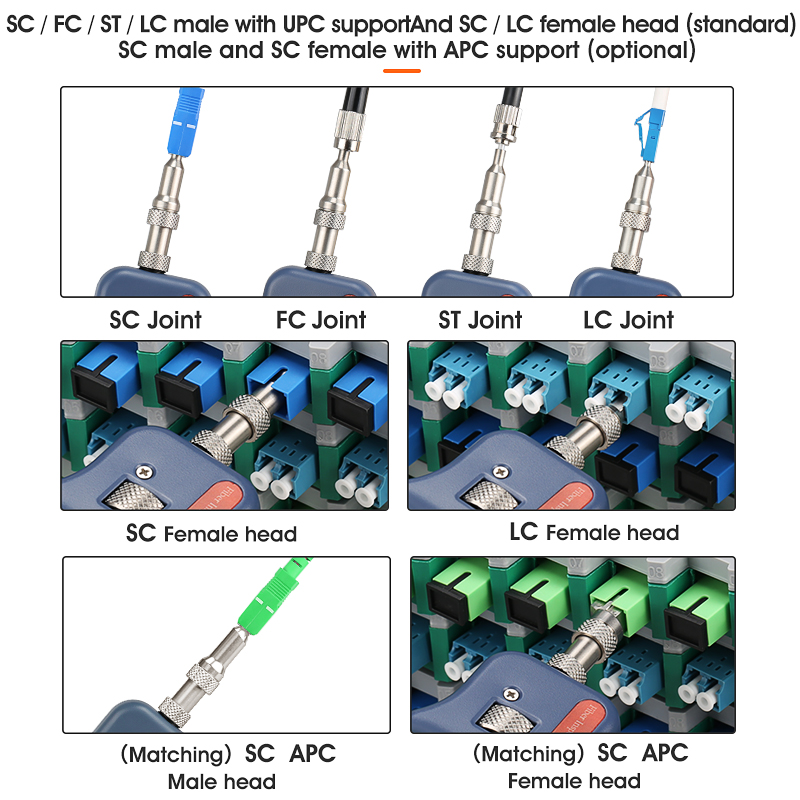
SC APC FAST CONNECTOR
Fiber Fast Connector is used for field assembled optical fiber connector, widely used in fiber to the home (FTTH) access optical networks, to assemble with drop cable quickly.
Circular Pole Clamp, hot dipped galvanized, CA type 5-7″ diameter
DVP 740 Fusion Splicer Machine
COMPTYCO AUA-400 Fiber Optic Inspection Microscope Probe with 3.5 inch Display Screen Monitor
Categories
- Cable TV and Internet Subscription
- Cable TV Equipment
- Coaxial Cables Transmissions
- Electrical
- EOC Technology
- EPON & GPON
- FIBER OPTIC CABLES
- Fiber Optic Tools, FTH Tools Equipment and Accessories
- FTTH Equipment and Accessories
- FTTH Tools
- Heavy equipment
- IPTV SOLUTIONS
- ISDBT Products
- Others
- Passive Fiber Optics
- Pole Line products
- Satellite Dish
- SFP, Routers, Switches, Server Cabinets and other Networking products
- Underground cabling equipments
Tags
- 1.25Gbps BIDI 40km 1310nm/1550nm LC wdm SFP Module
- 12 24 48 72 96 144 288 core figure 8 gytc8a cable fig 8 fiber optic cable gytc8s aerial cable
- 12f 24 48 96 72 144 288 FO fig 8 fiber optic cable Self-supporting aerial optical cable with 7 wires GYXTC8Y
- armoured submarine fiber optic cable
- Best Price Cental Tube MIni Figure 8 Aluminium Tape Armored Aerial Fiber Optic Cable with Stranded Steel Wire Messenger
- C-CORP Digital TV Receiver
- Cental Tube MIni Figure 8 Aluminium Tape Armored Aerial Fiber Optic Cable with Stranded Steel Wire Messenger
- Central Tube Figure 8 Fiber Optic Cable GYXTC8S
- CHT3554 48v lithium battery tester can replace HIOKI 3554
- Factory Supply Competitive Price Central Tube Figure 8 Fiber Optic Cable GYXTC8S
- Figure 8 steel tape armored Aerial Fiber Optic Cable Stranded Loose Tube fig 8 Optical Fiber Cable 8 core fiber optic cable
- fujikura
- fujikura 45s
- fujikura fusion splicer machin
- fusion machine
- fusion splicer
- GYFTC8Y 12 cores Figure 8 Aerial Outdoor Optical Fiber Cable Price per Meter Fig8 2000M per drum
- HDPE Microducts Connector
- High Voltage Operating Fiberglass Telescopic Hot Stick
- Huawei ONU HG8247H5 4GE + 2POTS + WIFI + CATV + USB Port GPON/EPON XPON
- lashing wire clamp
- lineman belt
- Manufacturing fibra optica figura 8 gyxtc8s 12 48 96 144 288 core aerial armored Optical Fiber Cable
- Metal Material Indoor and Outdoor Waterproof Wall Mounted 48 Core FTTH Fiber Optic Distribution box
- optica 4-24 core oplc 9/125 g652b g652d figure 8 fiber optic cable price GYTC8S GYTC8A Self-support Fiber Cable
- Optical Cable with HDPE She
- outdoor communication cable
- Outdoor overhead figure 8 Optical fibre cable 4 6 8 12 core fiber optic cable price Fig8 GYXTC8Y
- Outdo Optic Cable Price 32 48 64 72 96 144 288 coresor Waterproof Steel Armour Fiber Cable Anti-rodent Submarine Fiber
- PQWT GX800 Underground Pipe Locators RF Underground Wire Fault Detector
- safety belt
- ShinewayTech SLS-50A Stabilized Laser Source Fiber Light Source 1310 1550nm
- Single Mode Figure 8 Fiber Optic Cable
- SKYCOM T319S Full Function Fusion Splicer
- splicer machine
- ST620B TDR Cable Fault Locator with DMM function
- ST805C-X PON Power Meter
- sumitomo





























Reviews
There are no reviews yet.